Securing Your Website: A Strategic and Architectural Imperative
In today’s hostile digital landscape, a website is a primary target. It isn’t enough to just build a functional or beautiful site; you must build a fortress. A single vulnerability can lead to devastating data breaches, ransomware attacks, and the complete erosion of customer trust. Website security isn’t an “add-on” or a checkbox—it is the foundational layer of any serious digital overhaul and high-quality website building project.
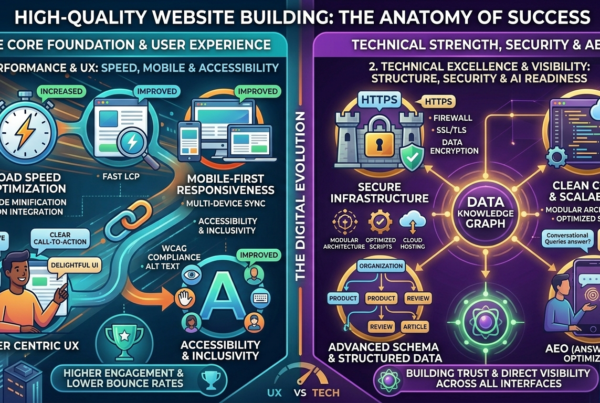
The provided infographic, “SECURING YOUR WEBSITE: A MULTI-LAYERED STRATEGY,” visualizes this comprehensive approach. It breaks down website security into two critical, interconnected domains: The Perimeter & Application Defense and Data Integrity & Proactive Resilience. This visual map highlights that true security isn’t a single product, but a constant, multi-layered process.

Pillar 1: Perimeter & Application Defense (Defending the Entry Points)
The first half of a robust security strategy is about defending the entry points and the application itself. This pillar is vibrant with energetic blues and oranges, symbolizing active defense and performance.
Secure Infrastructure & Encryption (The Essential Foundation)
The infographic places Secure Infrastructure at the very beginning. This is non-negotiable. High-quality building requires obsessive attention to foundational security:
HTTPS (SSL/TLS Certificates): Every website must encrypt data in transit. This prevents “man-in-the-middle” attacks where hackers intercept passwords or credit card numbers. It is also a critical trust signal for both users and search engines.
Web Application Firewall (WAF): A WAF is your first line of defense against common application-level attacks. It inspects incoming traffic and blocks malicious requests, protecting you from threats like SQL Injection, Cross-Site Scripting (XSS), and Cross-Site Request Forgery (CSRF).
Pillar 2: Data Integrity & Proactive Resilience (Protecting the Core)
The second half of the security strategy is about protecting the core data and ensuring business continuity. This pillar uses rich purples, golds, and glowing greens, conveying strength, value, and proactive intelligence.
Data Protection & Encryption at Rest
While HTTPS protects data in transit, you must also protect data at rest within your databases and file systems. High-quality building implements strong Data Encryption (e.g., AES-256) for sensitive information like user profiles, payment details, and proprietary business data. This ensures that even if a hacker breaches your server, the data they steal is unreadable and useless.
Code & Dependency Management (Defending from Within)
A fortress is only as strong as its weakest component. High-quality building means maintaining Clean Code & Scalability, which includes rigorous security audits:
Secure Coding Practices: Developers must be trained to write secure code, sanitizing user inputs and avoiding common vulnerabilities.
Dependency Scanning & Patching: Modern websites rely on numerous third-party libraries and plugins (dependencies). These are frequent vectors for attack. Continuous scanning and immediate patching of these dependencies are critical to closing known security holes.
Access Control & Identity Management
Who has access to your website’s critical infrastructure?
Strong Authentication (2FA/MFA): Require multi-factor authentication for all administrative accounts. This adds a crucial layer of security, even if a password is compromised.
Role-Based Access Control (RBAC): Grant users only the permissions they need to perform their job (the principle of least privilege). A content editor should not have the ability to modify server configurations or access user databases.
Vulnerability Scanning & Penetration Testing
You can’t patch what you don’t know is broken. Security requires a proactive, “red team” mindset:
Continuous Vulnerability Scanning: Automate regular scans of your website and server infrastructure to identify known security flaws, misconfigurations, and outdated software.
Periodic Penetration Testing: Hire ethical hackers to simulate real-world attacks. This uncovers complex, logic-based vulnerabilities that automated scans might miss, providing a deep assessment of your security posture.
Backup, Recovery & Continuous Monitoring
In security, you must always prepare for the “when,” not the “if”:
Robust Backup & Disaster Recovery (DR): Maintain regular, automated, and off-site backups of all website data and configurations. A well-tested disaster recovery plan ensures you can quickly restore your site to a known good state in the event of a ransomware attack or data corruption, minimizing critical downtime.
Real-Time Security Monitoring & Alerting: Implement comprehensive logging and continuous monitoring. This allows you to detect anomalous behavior, potential brute-force attacks, or successful breaches in real-time, enabling immediate incident response.
Conclusion: Trust is the New Visibility – Choosing the Path of Strategic Excellence
The infographic “SECURING YOUR WEBSITE” is a definitive multi-layered map. The Perimeter & Application Defense pillar focuses on blocking attacks and validating trust at the entry point. The Data Integrity & Proactive Resilience pillar focuses on protecting your most valuable asset (your data) and ensuring your business can withstand and recover from a successful breach.
Building high-quality isn’t just about speed, UX, or AI readiness (AEO). It is, above all, about Technical Excellence & Visibility built on a secure foundation. A compromise in security invalidates all other achievements. By building your digital overhaul on both pillars of security, you create a future-proofed, resilient business platform that protects your customers, your data, and your long-term reputation. Choose the path of strategic, architectural excellence.